Who Has Access to Your Business Right Now?
Most security issues don’t start with a breach. They start with access that no one is actively thinking about.
An old employee account still active.
A personal device connected to company email.
Too many people with access to financial systems or shared files.
It only takes one gap to expose sensitive data, interrupt operations, or create a compliance issue.
This checklist helps you find those gaps quickly.
Get Your Free Checklist
Employee Security Risk Assessment: Devices & Access Exposure
Your systems may be protected, but access and devices are where risk tends to slip through.
This checklist helps you review how employees access systems like email, file sharing, CRM platforms, and financial tools, and where exposure may exist.
✅Takes 5–10 minutes to complete
✅Easy to review with leadership or IT
✅Built for real-world Baltimore businesses
Enter your email to get instant access.
No spam. Just a practical tool you can use right away.

Employee Access Risks Add Up Quickly: Find the Gaps Before They Cause Problems
Access risk doesn’t usually come from one big mistake.
It builds over time as teams grow, roles shift, and new tools are added.
You’ll get a clear view of where things stand in under 10 minutes.
This checklist helps you:
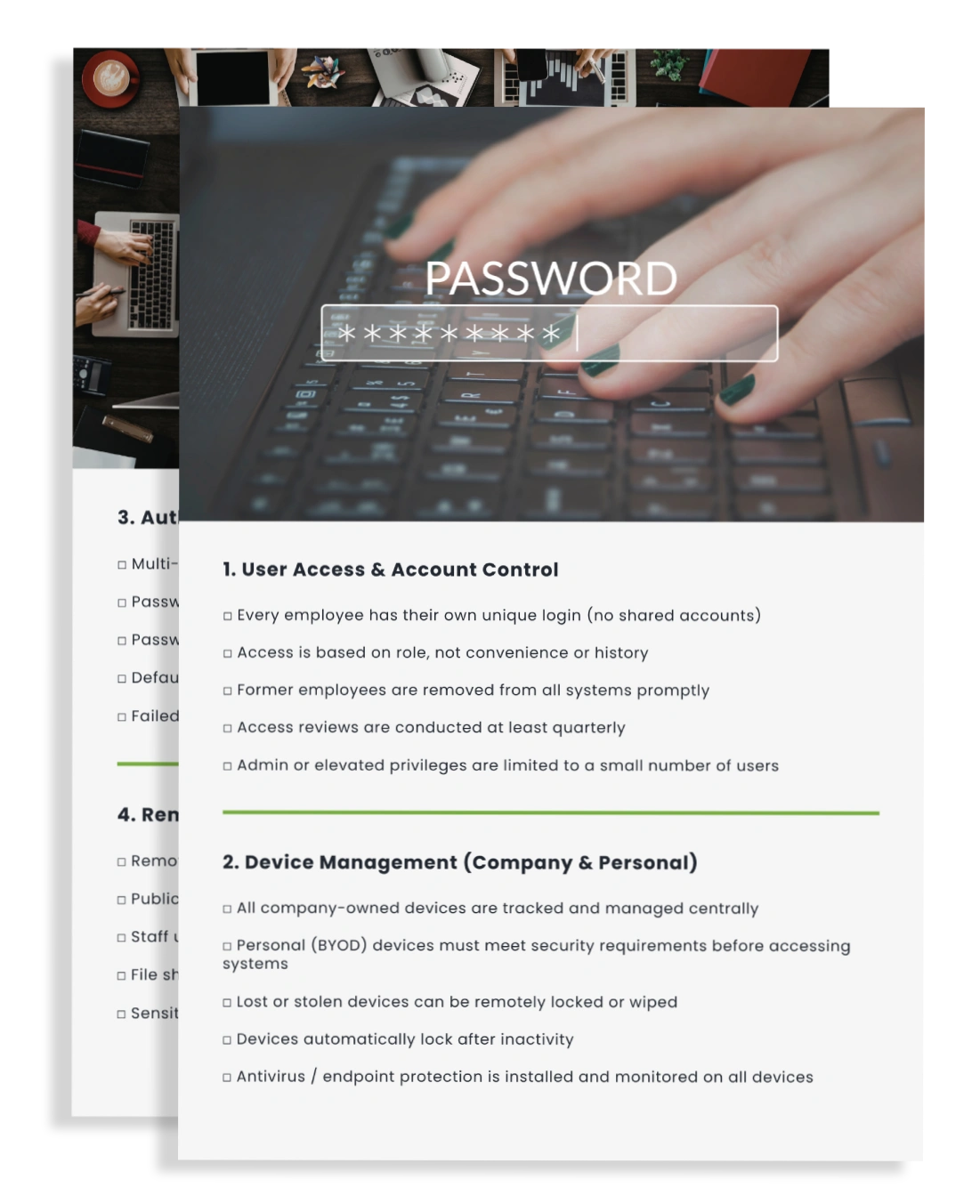
Identify leftover access from former employees or role changes
Understand how unmanaged or personal devices create exposure
Spot habits like shared logins or inconsistent security practices
Reduce the risk of data loss, downtime, or unauthorized access
You’ll get a clear view of where things stand in under 10 minutes.
What This Employee Access & Device Security Checklist Reveals About Your Risk
No technical deep dive required. Just clear, usable insight.
A structured checklist covering access, devices, and employee behavior
Clear sections you can review quickly with your team
A scoring system to show where you stand today
A simple way to flag risks and decide what to address first


Most Businesses Already Have These Access Risks: Here’s What Typically Gets Missed
During most security reviews with Baltimore-area organizations, the same patterns tend to show up:
Accounts that were never fully removed
Personal or unmanaged devices with access to company systems
More people with access than expected
Limited visibility into login activity
These aren’t unusual. They’re what happen when systems evolve over time.
This checklist helps you surface those gaps before they turn into something disruptive.

How Baltimore Businesses Get Control Over Employee Access and Device Security
At OmegaCor, we help Baltimore businesses get control over access, devices, and security without adding unnecessary complexity.
From access management and endpoint protection to compliance and ongoing monitoring, we focus on making your environment easier to manage and easier to trust.
Our role is simple: help you see where the risks are and give you a clear path to address them.
“OmegaCor helped us get control over user access and devices across our entire team. It brought clarity and calm to an area of the business that had become chaotic and hard to track.”
– Nonprofit Client, Baltimore
Find Out Where Employee Access and Devices Are Putting Your Business at Risk
If access and device security feels unclear or inconsistent, this is a good place to start.
